Application Modernization

Use the newest technology stack to make your applications more agile, efficient, and future-ready
Adopting new technologies, frameworks, architecture, and infrastructure platforms, and integrating with new features and functionalities that can provide technical innovations with changing business trends are all part of the process of updating legacy applications into newly transformed applications. This is the process of legacy application modernization.
Our all-inclusive legacy application modernization services offer business agility, scalability, and a better user experience. Organizations of all sizes should implement a flexible transformation plan for their applications and data.
Our Capabilities
Digital transformation represents technological growth. Organizations are embracing new emerging technologies such as AI/ML, Big Data, Data Analytics, IoT, Blockchain, RPA, Cloud, and Mobility to boost revenue, improve customer satisfaction, and minimize time-to-market. Batch processing time is decreased by 33% through performance improvement of large databases.
Strategies for Application Modernisation
Categorizing Applications with the 6R Approach
The 6R approach categorizes your application into six strategies: Re-host, Re-platform, Re-factor/Re-architect, Re-purchase, Retire, and Retain.
The important component of the 6R framework is the collection of application portfolios and separation based on environment, interdependencies, technological difficulties, and a migration mechanism.
We provide a clear migration plan for each application in your portfolio based on customer needs. As we learn more about your whole environment and interdependencies, we iterate and develop the plan. The complexity of migrating varies according to architecture, license agreements, and business requirements.

-
Benefits of Application Modernization Services -
Streamlining Business Processes for Time to Market
01Businesses can simplify and automate their processes, making it easier to deliver products and services to market quickly.
-
Mechanism of Increased Revenue
02Enhance customer experiences and drive revenue growth through improved user engagement, higher conversion rates, and increased sales.
-
Proper Software Documentation
03Improve the quality of software documentation, making it easier for businesses to understand how applications work and how they can be improved.
-
Scalable and Robust Application
04Helps businesses build scalable and robust applications that can handle increasing amounts of data and traffic, making them more adaptable to future business needs.
-
Boost Operational Effectiveness
05Improve the performance and functionality of applications, leading to greater efficiency and productivity for businesses.
-
Higher Performance
06Helps businesses optimize application performance, leading to faster response times, reduced downtime, and improved user satisfaction.
-
Flexible UI/UX
07Helps businesses create more flexible and user-friendly interfaces, leading to better user experiences and increased customer satisfaction.
-
Lower Maintenance Cost
08Reduce the cost of maintaining legacy systems by making them easier to maintain and support, reducing the need for costly manual interventions.
-
Tailored Solutions
01Experts help businesses assess their current systems and suggest modernization strategies for better efficiency, scalability, and cost-effectiveness.
-
Mechanism of Increased Revenue
02Migrating data from outdated, disparate, or unstructured data systems to modern databases, providing better data management and accessibility.
-
Proper Software Documentation
03Moving applications from one platform to another, such as from on-premise to the cloud, improving availability, scalability, and security.
-
Application Modernization Services
Execution Methodology
-
Goal Definition
Market and technology analysis Define stakeholder vision Budget for modernization
-
Market and technology analysis Define stakeholder vision Budget for modernization
Priority List for Modernization/ Current State Assessment / Re-Assess
-
Discovery/Approach Agreement
Choose the technology stack Choose best tools & techniques Develop test plans
-
Document Milestones Document Cost Estimates
Review of costs and planning
-
Execution
Staff project team Execute migrations, security assessments, & testing Report status to stakeholders
-
Support & Maintenance
Future
Alliances & Partners

Why Us?
Our Value Multipliers
Digital transformation requires the right blend of business acumen, people, and technologies. Our global team of experts are experienced in a multiverse of different technologies. Our service models to assess and deploy the most sought after technologies mentioned below to perfectly fit your business needs:
-
Microsoft
-
Emerging
-
CMS
-
Open Source
-
JS Framework
-
Testing
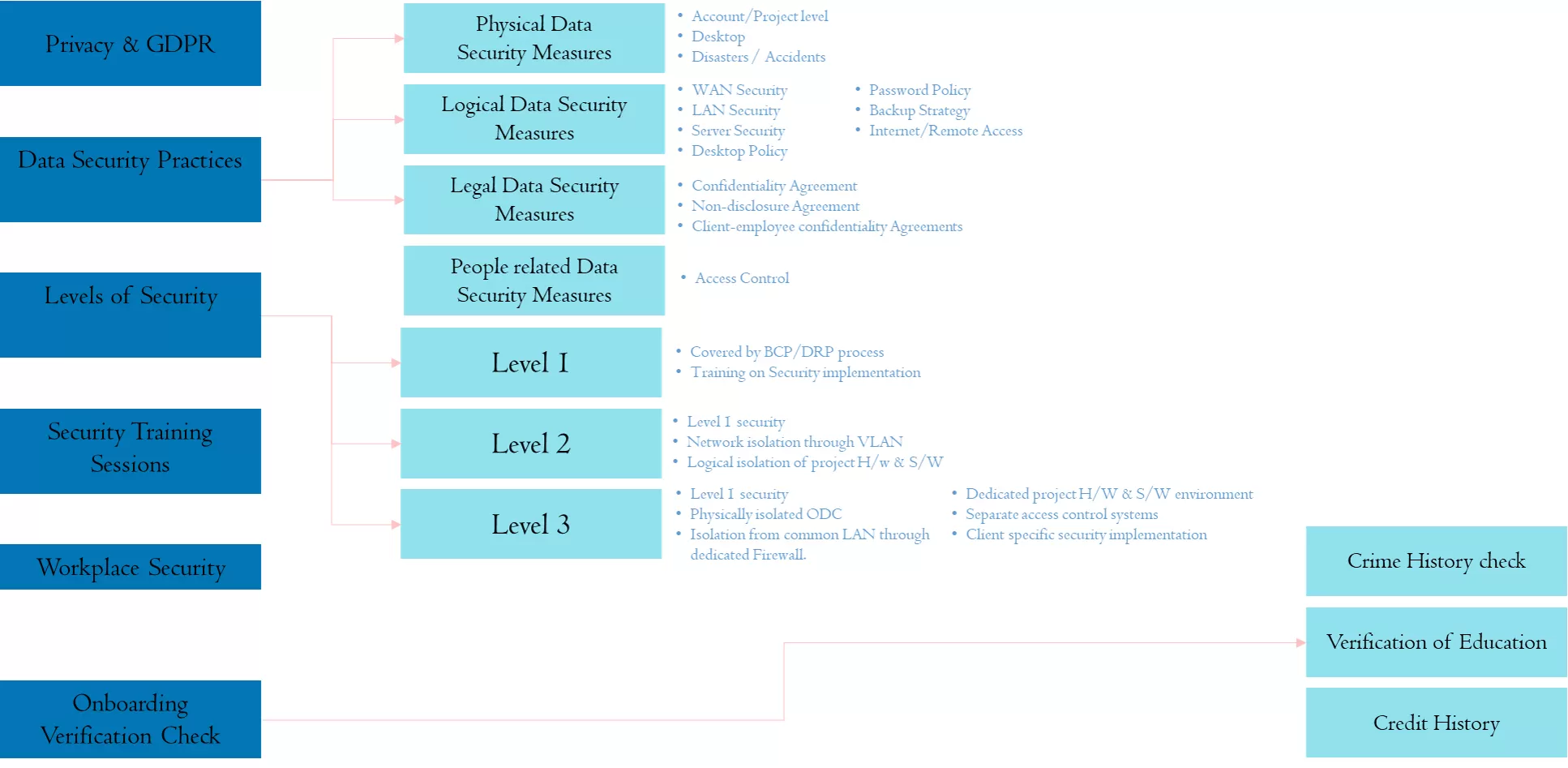
We believe in a comprehensive security system. We ensure the best in class security right from following GDPR guidelines, data security practices to adhering to strict guidelines at the workplace.
These are three core objectives of our Security Policies:
Confidentiality – Protection of assets and networks from unauthorized users.
Integrity – Ensuring that the modification of assets is handled in a specific and authorized manner.
Availability – Ensuring continuous access to assets and networks by authorized users.
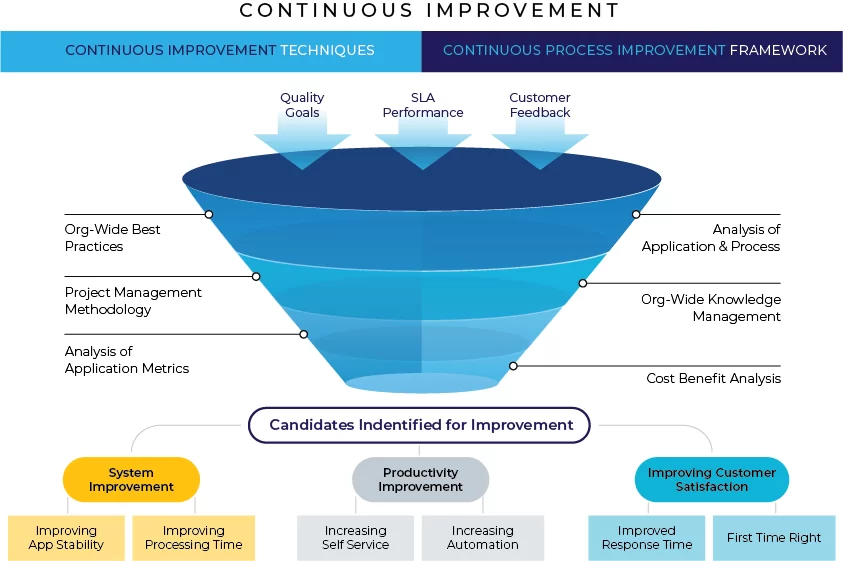
We believe in constantly pushing our boundaries. Continuous improvement is important because it’s the best way to ensure that we’re doing things in the most efficient, effective, and productive way, every single day of the week, and on every single component that we’re working on.
Responsiveness (Manage and Measure)
Improve Incident management (Jira)
Better Ticket Documentation
Review and corrective action on Aging of tickets
Capture Voice of Customer
Identify Improvement areas
Process Changes – Apply Lean
Root Cause and Causal Analysis (Improve and Maintain)
Mandate RCCA comments for closed tickets
Maintain Database and Prioritize ‘Maximum Impact’ RCCA
RCCA Report-outs
Cost Reduction YoY with no change in Capacity
Support Ticket Reduction (Create Win-Win situation)
Baseline the number of tickets at project kick-off
Re-baseline every end of Qtr.
Incorrect ticket closures
Application Stability
Team will analyze the batch process and look at the opportunity of Process improvements
Reduction of the run time of batch will reduce mainframe utilization
Post Facto Review –OC team can inspect/Review for code changes already moved to further reduce the risk of having bad code in production
Meet Progressive Demand
Evaluate trend based on Historical Data
Projections start in the second month of the Qtr.
Pool of resources
Monthly meeting on capacity loading
Quarterly meeting for capacity adjustments
Second month of the quarter Load shadow resources
Induct incremental resources
Connect with Us
Book A DemoInsights
INDUSTRIES
PLATFORMS
SERVICES
CONSULTING
- AlvariumTM - Design Led ConsultingOpens a new window
- Digital Marketing Services
- Automotive Aftermarket
- Digital Logistics
- Remote Engineering
PROFESSIONAL SERVICES
DIGITAL
FUTURE ENGINEERING
Let's Talk
Book a Meeting
We value your privacy.
This website uses cookies and similar technologies to improve your browsing experience, measure our audience, collect useful information, and provide you with relevant content. By selecting “Accept & Continue”, you confirm that you provide your consent for the use of your information, and have read and agree to our Privacy Policy , and Terms of Use.DeclineAccept & ContinueCookie settings
Privacy Overview
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |